Crypto Scams
Crypto Scams: How Arkose MatchKey Bankrupted the Efforts of a Russian Hacker
“My partners and I lost time and money while Arkose Labs introduced new precautions on Twitter.” – anonymous spammer
In the digital landscape, social networks are tirelessly combating fraudulent bot accounts that inundate users with direct messages and attempt to lure them into deceptive cryptocurrency investment platforms. The FBI now suggests financial losses from cryptocurrency investment scams dwarfed losses for all other types of online crime in 2022, rising from $907 million in 2021 to $2.57 billion last year.
According to a recent interview with a crypto scam investment spammer, a series of aggressive campaigns recently forced several Mastodon communities to halt new registrations, causing both financial and customer-related problems. Numbers now reveal, these scams are currently earning more than $2,000 over a week by selling some 100,000 private mentions to Mastodon users in different communities.
While these attacks were greatly deterred by the introduction of CAPTCHA challenges, one anonymous Russian spammer went on record to say it was actually the challenges of Arkose MatchKey that “put a crimp” in his earnings on the social platform Twitter.
The anatomy of a crypto scam
A crypto scam on a social network happens when bad actors attempt to deceive users and manipulate them into sending cryptocurrency, such as Bitcoin or Ethereum, to their wallets. These scams take advantage of the popularity and fast-paced nature of social media platforms to spread quickly and target unsuspecting users. Aside from the standard tactics of impersonation and fake giveaways, scammers also use these strategies to implement attacks:
- Phishing attacks: Scammers may share links on social media platforms that appear to lead to legitimate crypto-related websites, wallets, or exchanges. However, these links are cleverly designed to trick users into entering their sensitive information, such as login credentials or private keys. Once users provide this information, scammers can access their accounts and steal their funds.
- Malware and fake apps: Some scammers create malicious software or fake mobile apps that mimic legitimate cryptocurrency wallets or exchanges. They promote these apps on social media, enticing users to download and use them. Once installed, these apps can steal sensitive information or gain unauthorized access to users’ wallets.
- Pump and dump schemes: In this type of scam, scammers artificially inflate the price of a lesser-known cryptocurrency by spreading false information or rumors about it on social media. They might create hype around a particular token, urging users to invest quickly to make huge profits. Once the price rises due to increased demand, scammers sell their pre-purchased tokens at the inflated price, causing the price to crash, and leaving other investors with losses.
Crypto scams vs. CAPTCHA
In the words of a programmer working on the Mastodon project, crypto scams like this can unleash a “spam torrent targeting users via private mentions,” a kind of direct messaging on the platform. Using more than 1,500 internet addresses across 400 providers to register new accounts, spammers created messages telling recipients about bogus investment credits on a crypto trading platform. The attack model was so popular, the volume of bot accounts being registered for the crypto spam campaign started overwhelming the servers that handle new signups.
When new account registrations on Mastodon were disabled, the servers came under a sustained distributed denial of service (DDoS) attack that lasted three hours, non-stop, 200,000 to 400,000 requests per second. Since Mastodon social has been retrofitted with a CAPTCHA-based solution, the spam waves have finally died down.
Although not directly aimed at mitigating DDoS attacks, CAPTCHAs can be employed as part of a multi-layered defense strategy to protect against these threats. Website owners can implement CAPTCHAs as an additional step in the user authentication process, aiding in the identification and blocking of malicious bot traffic. By differentiating between legitimate users and automated attack traffic, CAPTCHAs reduce the overall impact of a DDoS attack.
Hacker Touts Efficacy of Arkose MatchKey
But are CAPTCHAs really the best solution? According to an anonymous Russian hacker who makes “telegram bots and other rubbish cheaply,” the answer is no. It was only the challenges of Arkose MatchKey that finally put a crimp in his illicit earnings. While conversion rates for bot-powered direct message spam are high, these same numbers on social networks are far more profitable for spammers. As a result, spamming people with invitations to cryptocurrency scams pays more than legitimate programming jobs that don’t involve malware and botnets.
With 70% less friction than CAPTCHA, the challenges of Arkose MatchKey made the difference in thwarting these types of threats. In the spammer’s own words, “My partners and I lost time and money while Arkose Labs introduced new precautions on Twitter.” The implementation of new precautions by Arkose MatchKey caused significant setbacks for this malicious actor and their partners, resulting in the loss of valuable time and financial resources.
Arkose MatchKey is an advanced security solution that offers a significantly reduced level of friction compared to traditional CAPTCHA systems. CAPTCHA is a common method used to distinguish between human users and automated bots, but it often presents challenges for users, leading to frustration and potential abandonment of online activities.
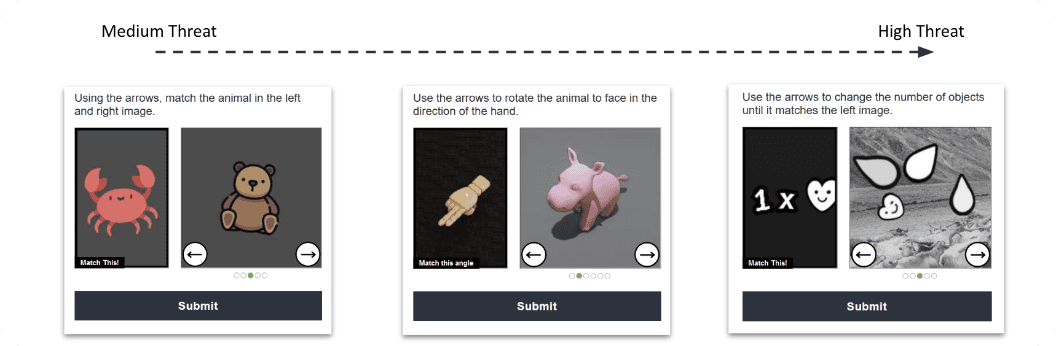
Arkose MatchKey’s innovative approach provides a more user-friendly experience while effectively countering threats posed by malicious actors. By utilizing sophisticated challenges that are difficult for automated bots to solve, Arkose MatchKey ensures a high level of security without burdening legitimate users.
Try the Arkose Matchkey puzzles!
In short, Arkose MatchKey’s advanced security measures, with its reduced friction, successfully hindered the hacker’s attempts to exploit vulnerabilities on the Twitter platform. By introducing new precautions, Arkose Labs demonstrated their commitment to enhancing online security and protecting users from various threats, ultimately leading to the hacker’s frustration and financial losses.
Looking to protect your organization from spam and abuse? Speak to an expert today to learn more.
*** This is a Security Bloggers Network syndicated blog from Arkose Labs authored by Jenn Jeffers. Read the original post at: https://www.arkoselabs.com/blog/crypto-scams/